FLYING FOX ENTERPRISE®
Flying Fox® Enterprise is an innovative security solution that accurately detects identifies, and locates wireless security threats and seamlessly integrates into any organization's security operations.

usage
Definitive Monitoring
Get "Always on" monitoring and playback so no devices are missed. Our proprietary decoding techniques eliminate false alarms.
Beyond Traditional WIDS
Go beyond monitoring just WiFi devices with detailed insight into all types of Bluetooth and cellular devices.
UI Built for the Operation
Flying Fox® Enterprise hides the complexity of spectrum and protocol so you can focus on accurate detection and location info to find and mitigate threats.
Benefits
THE #1 CHOICE FOR FEDERAL OPERATIONS
Developed in collaboration with a Naval Research Laboratory, Flying Fox® is the wireless security solution protecting the security of critical federal operations. Meet your PED policy compliance, such as AR 380-28 and DHS MD 11021.
AN EASILY SCALABLE SOLUTION
Catering to deployments from portable conference room setups to campus-wide installations, Flying Fox® multi-floor, multi-building capable UI-plus its simple integration with enterprise SIEM tools-allow it to grow with your needs.
about+demo
WATCH FLYING FOX® IN ACTION
Our user-centric UI simplifies complex wireless security tasks and offer real-time insights into signals of interest, allowing you to separate trusted devices from unknown devices and locate and take action against possible threats. Customizable controls make it easy to adapt to various user needs, from beginners to experts.
case study















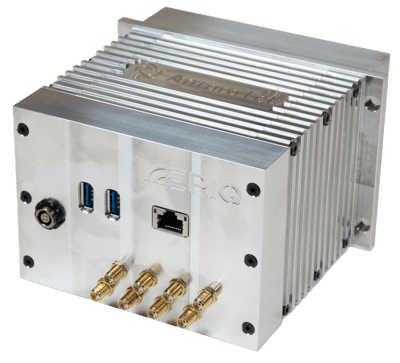
.webp?length=400&name=Cyber-Radio-NDR585%20(3).webp)

















.webp?width=70&height=70&name=Vector%20(1).webp)




